
Phishing: the question is not if you fall for it, but when
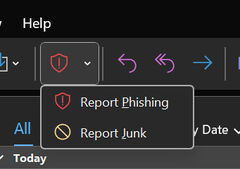
Do you know what that button with the little red shield in Outlook is for? Information security officer Stan van Aarle hopes more and more members of the TU/e community will start clicking it whenever they receive a suspicious email. The button helps the system intercept phishing attempts. “We need everyone’s help to keep TU/e’s data safe.”
Stan van Aarle calls the strategy a “human firewall.” “If a lot of staff and students report the same email via the button in Outlook, the system can perform an initial analysis on its own and automatically block similar emails sent to other TU/e addresses,” he explains. This process is monitored by the Security Operations team, Van Aarle emphasizes.
Van Aarle is passionate about his job as an information security officer at LIS. Together with his colleagues, he sees it as their mission to raise cybersecurity awareness among the TU/e community. “We need everyone’s help to keep TU/e’s data safe,” he stresses. That is why, with the help of an external partner and in consultation with Security Operations and (departing) CISO Martin de Vries, he regularly sends out fake phishing emails to a random sample of students and staff.
What is phishing?
PhiPhishing is a form of online fraud in which cybercriminals “fish” for sensitive information — yours, or TU/e’s — by pretending to be a trustworthy party, such as a well-known company. But why spell it with ph? That comes from hacker slang.
Phishing is a type of social engineering: tricking people into giving away information by exploiting human traits such as curiosity, trust, or fear. You can find tips on spotting phishing emails for example at Microsoft Support.
A targeted variant is spear phishing. In these cases, cybercriminals deliberately go after specific information — for example, sensitive scientific data — by researching someone’s background and trying to earn their trust.
Courier service
Imagine quickly working through your inbox, and before you realize that an email claiming to be from HR isn’t really from HR, you’ve already clicked a link. Should you feel embarrassed as a tech-savvy TU/e student or employee? “Absolutely not,” Van Aarle stresses. “The question is not if you’ll fall for it, but when. It happens to everyone at some point.”
Hackers do everything they can to catch you off guard: sending emails late in the workday when you’re tired and in a rush, or investigating which applications TU/e uses, so they can choose them as fake senders. “It’s also a matter of bad luck: if you’re waiting for a message from HR, or a delivery notification from a certain courier service, you’re more likely to click on an email that appears to be from that sender.”
And that’s not the end of the world, Van Aarle adds: “What matters most is getting into the habit of consistently reporting suspicious messages.”
A cat-and-mouse game
By sending out fake phishing emails — harmless ones, fortunately — the Security Operations team helps keep the TU/e community alert. And up to date, because cybercriminals are constantly coming up with new tricks in their cat-and-mouse game with internet users.
“Every two months we update the test emails to reflect current threats,” Van Aarle says. At the moment, “infostealers” are trending among hackers: malicious software that, after just one click on a tempting link, scans your computer for login credentials and other private information — all without you noticing.
“We also want to make the test phishing emails gradually harder to recognize. Right now there are still multiple red flags — spelling mistakes or a strange sender address — but we’re reducing those.” The goal is to make the TU/e community increasingly resilient against phishing attempts.
Anyone who clicks on a test email, or for example forwards it to a colleague, receives an invitation to brush up on their skills with a short instructional video.
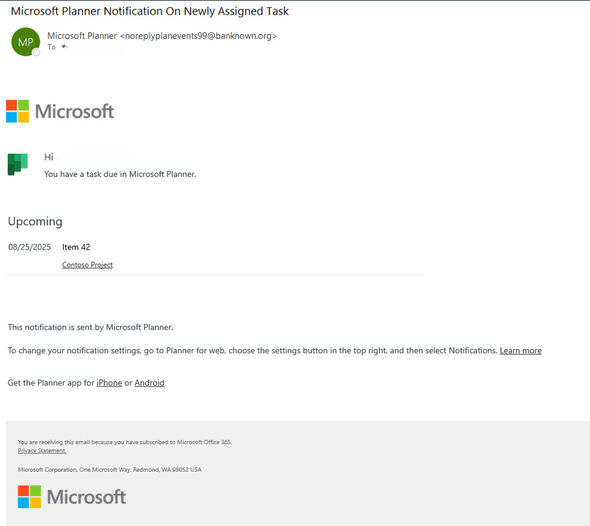
Microsoft Planner
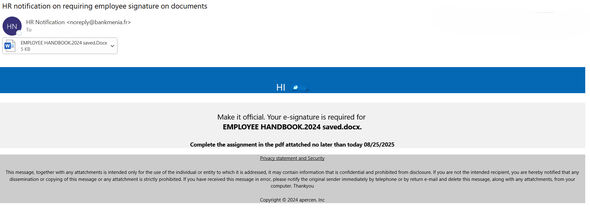
Van Aarle pulls up the data from phishing simulations sent in June and July to over 5,000 TU/e students and almost as many staff members. Students received a fake notification from Microsoft Planner, an application they use to manage group project tasks. Staff received an email supposedly from HR, asking them to sign a document.
The students seemed slightly more alert than staff: 14 percent of students clicked on the link in the Planner email, compared to 18 percent of staff who clicked on the HR message. That’s better than last summer, when an earlier test email fooled 39 percent of recipients. “But those percentages aren’t directly comparable, because it was a completely different phishing campaign,” Van Aarle points out.
Report button
And what about reporting phishing emails? 27 percent of staff used the report button in Outlook, versus only 4 percent of students. Van Aarle hopes to see that last figure rise. “Our goal is for an average of 30 percent of recipients to report the test emails by the end of 2025,” he concludes.
Eerste hulp bij Phishing
What should you do if you receive an email in your TU/e inbox that you don’t trust?
- Select the email in Outlook and click the button with the red shield-and-exclamation-mark icon in the toolbar (see image).
- Did you only realize after clicking through—and possibly filling in your personal details—that you might have fallen victim to a phishing attempt? Or is your computer suddenly acting strangely? If so, please contact the LIS service desk by calling 2000 or sending an email to lisservices@tue.nl.
- Have specific questions about phishing? Send a message to abuse@tue.nl. (This address was previously used to report suspicious emails, but now the shield button is preferred.)
This article was translated using AI-assisted tools and reviewed by an editor.

Discussion